Section 3.4: Buffer Overflow Attack: Attack Techniques 1 PowerPoint Presentation, Free Online Download PPT VZFVHQ

SUNY at Buffalo; Computer Science; CSE620 – Advanced Networking Concepts; Fall 2005; Instructor: Hung Q. Ngo 1 Agenda Last time: finished brief overview. - ppt download

Matthew Hall on Twitter: "Also... not really “full stack” if memory corruption vulns aren't considered at all... some may say “yeah but when was the last time you found a buffer overflow
![Motorcycle Passenger Tossed Around Like Ragdoll in Buffalo Attack in South Dakota [Video] | lovebscott.com Motorcycle Passenger Tossed Around Like Ragdoll in Buffalo Attack in South Dakota [Video] | lovebscott.com](https://www.lovebscott.com/wp-content/uploads/2020/08/7b64f4334f4b428bb3d09c22a99be882_md-1280x720.jpg)
Motorcycle Passenger Tossed Around Like Ragdoll in Buffalo Attack in South Dakota [Video] | lovebscott.com

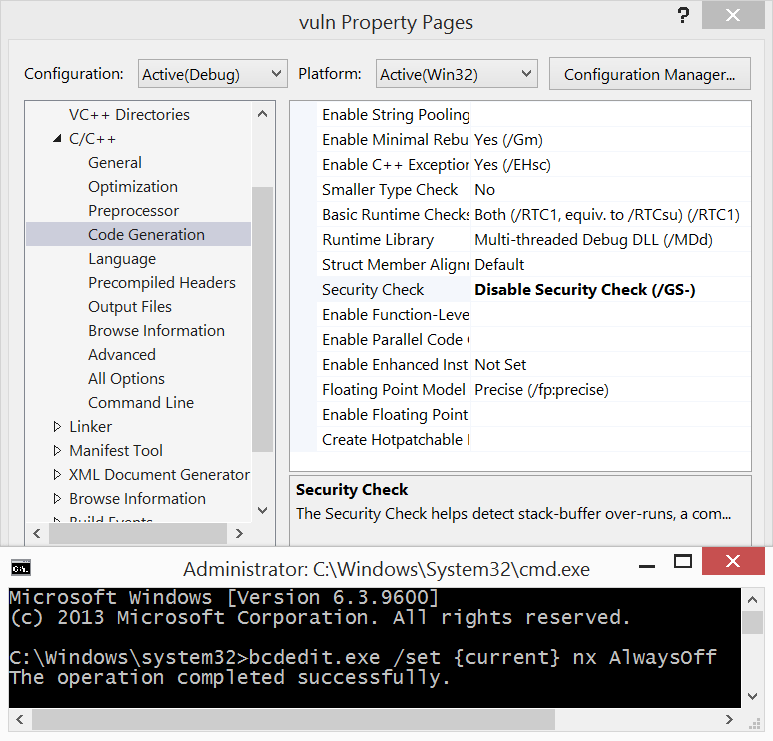
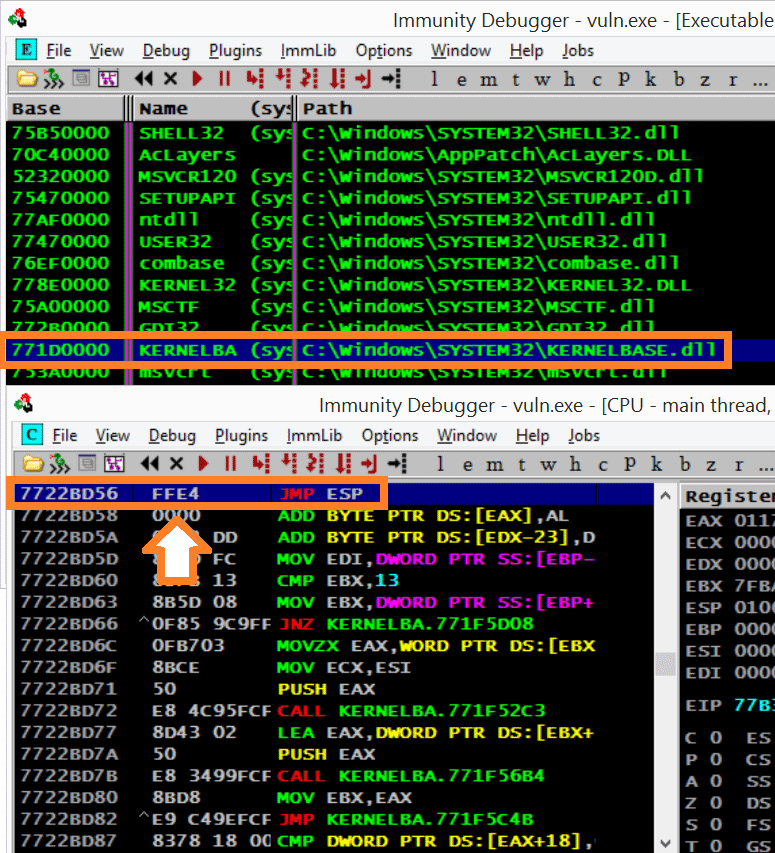
An introduction to computer buffer overflow problem on using unsecured C or C++ standard functions in C programs